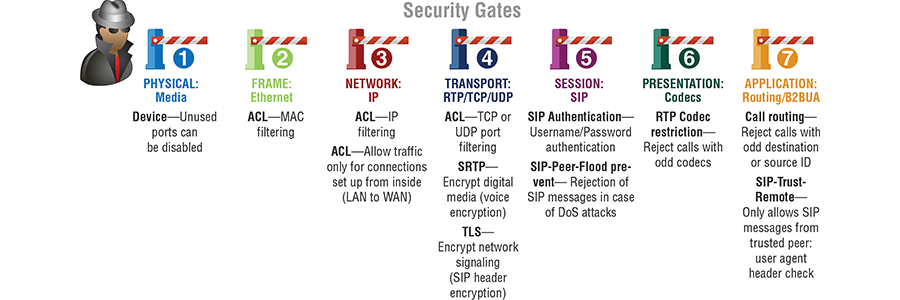
Network protection is serious business. Anywhere there’s a hole in a network security “fence” or “gate” some snooper, hacker or toll-fraud thief is going to find it. A good, solid network protection strategy builds a series of security “gates” at multiple layers within the OSI model.
Voice-over-IP technology has given birth to several daughters:
- unified communications
- SIP trunking
- hosted (IP) PBX
- cloud telephony.
These developments offer features that boost workforce productivity while offering streamlined, flexible network architectures and reductions in capital expenses (CapEx) and operating costs (OpEx).Sadly, the ALL-IP revolution also has a downside. Converged communication networks widen the attack surface for malicious players on the Internet. IP telephony opens the enterprise network to such vulnerabilities as toll fraud, denial of service (DoS) and distributed denial of service (DDoS) attacks, among others.
With toll fraud, the company may never notice the intrusion until the exorbitant phone bill comes in. With DoS/DDoS the loss of network resources is quickly apparent, yet the disruption of business operations is costly, and may take hours or days to resolve.
We propose an enterprise network security solution for SIP (session initiation protocol) based VoIP telephony with SIP trunking service delivered by an Internet telephony service provider (ITSP).
The proposed solution relies on an enterprise session border controller (eSBC) installed as customer premise equipment (CPE) at the subscriber location.
For details about this solution get the new Patton White Paper:
>>Secure All-IP Telephony

